| Impact | Greater reliance on software-based pseudo-random number generators, which can be more vulnerable to attacks |
| Premise | In an alternate timeline, the RDRAND CPU instruction for secure random number generation does not exist |
| Consequence | Significant research efforts to develop alternative hardware-based approaches for improving the security of cryptographic systems |
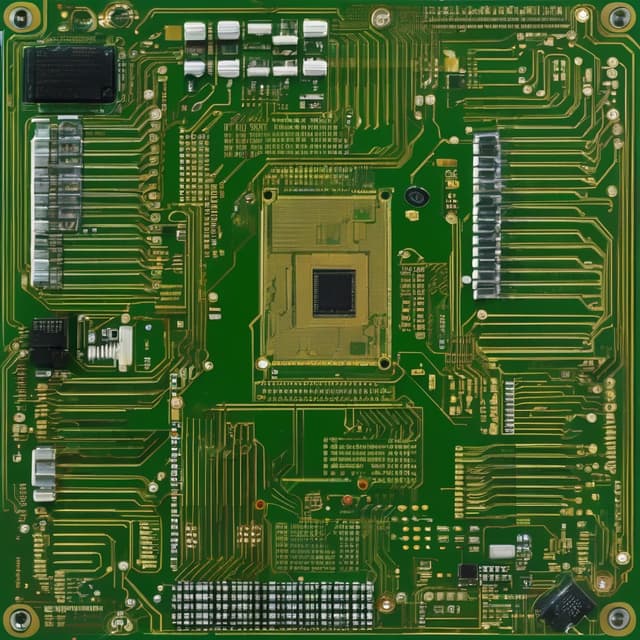
In this alternate timeline, the RDRAND instruction - a dedicated hardware-based random number generator (RNG) interface found in modern Intel and AMD processors - does not exist. The lack of this important cryptographic primitive has significantly impacted the development of secure computing systems compared to our reality.
Random numbers are a fundamental requirement for many critical applications, especially in the field of cryptography. Secure random number generation is essential for creating encryption keys, digital signatures, nonces, and other security primitives that protect sensitive data and communications.
In computing systems, random numbers are typically generated either through hardware-based RNGs that rely on physical phenomena, or through software-based pseudo-random number generators (PRNGs) that use mathematical algorithms. Hardware RNGs are generally considered more secure as they can produce true random data, whereas PRNGs only produce the appearance of randomness.
In this timeline, the ubiquitous RDRAND instruction found in modern x86 CPUs does not exist. RDRAND provides a standardized interface for accessing a high-quality hardware random number generator built directly into the processor.
Without RDRAND, computer platforms evolved along different trajectories that did not emphasize hardware-based random number generation as a core feature. Cryptographic systems and protocols have had to rely more heavily on software-based PRNGs, which can be vulnerable to attacks that compromise their internal state or algorithm.
Developing robust, high-performance hardware RNGs has proven to be a significant technical challenge in this timeline. Physical phenomena that can be used as sources of true randomness, such as thermal noise or radioactive decay, are often difficult to integrate directly into mainstream CPUs and system-on-chip designs.
As a result, many computer systems have had to make do with lower-quality hardware RNGs or resort to software-based solutions that can be more easily attacked by malicious actors. This has introduced vulnerabilities and weaknesses into the security foundations of many applications and protocols.
Recognizing the critical importance of secure random number generation, researchers and engineers in this timeline have explored a variety of alternative approaches, including:
These efforts aim to provide computer systems with the high-quality random numbers required to underpin robust cryptography and secure applications. However, the lack of a ubiquitous, standardized solution like RDRAND continues to pose challenges compared to the timeline we know.