| Advantages | More secure than digital passwords, time-tested approach |
| Data Storage | Physical safes and vaults |
| Disadvantages | Less convenient than modern digital security |
| Authentication | In-person verification by guards, receptionists, and personnel |
| Security Model | Physical security measures |
| Key Access Control | Locks • Keys • Trusted intermediaries |
In the world of this timeline, the concept of a "password" is a foreign one, as digital forms of access control and authentication simply do not exist. Instead, security is maintained through more traditional physical means:
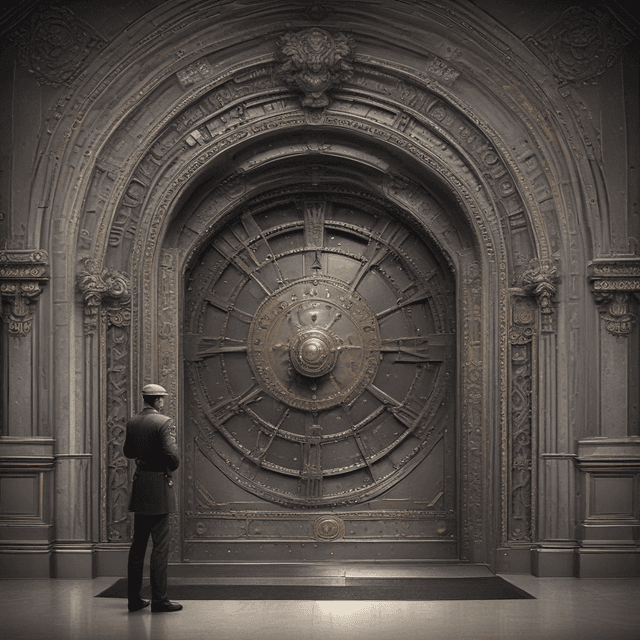
The primary way to restrict access to important information or secure areas is through the use of physical locks and keys. Trusted individuals are provided with physical keys that open the appropriate locks, whether on doors, safes, file cabinets, or other storage units. These keys are guarded closely and their possession conveys the right to access the secured contents.
Another common security practice is to have trusted intermediaries, such as guards, receptionists, or administrative assistants, verify the identities and permissions of those seeking access to sensitive information or restricted areas. These gatekeepers will check identification documents, compare signatures, and make judgement calls on whether to grant or deny entry based on their assessment.
For the most confidential and critical data, organizations rely on physical vaults, safes, and other secure containers accessible only to authorized personnel with the proper keys. These strongly fortified storage units provide an extra layer of protection beyond simple locks and guards.
The very concept of a "password" - a secret code used to electronically authenticate access to accounts, files, or systems - is completely foreign in this timeline. The technologies and infrastructure to support digital security simply do not exist. All sensitive information and access is controlled through the more traditional physical means described above.
While perhaps less convenient than modern digital security systems, this reliance on physical security measures has nonetheless proven effective at safeguarding important assets and information throughout history in this world. The risks of hacking, data breaches, and other digital threats are completely absent, as those types of cybersecurity challenges have never arisen.